In today’s rapidly evolving digital landscape, reliable and secure data access is more critical than ever. At first glance, database connectors—such as ODBC and JDBC—may seem like commodities, often bundled with DBMS platforms at no extra cost. However, this perspective overlooks the profound complexities these tools address and the intrinsic value they provide.
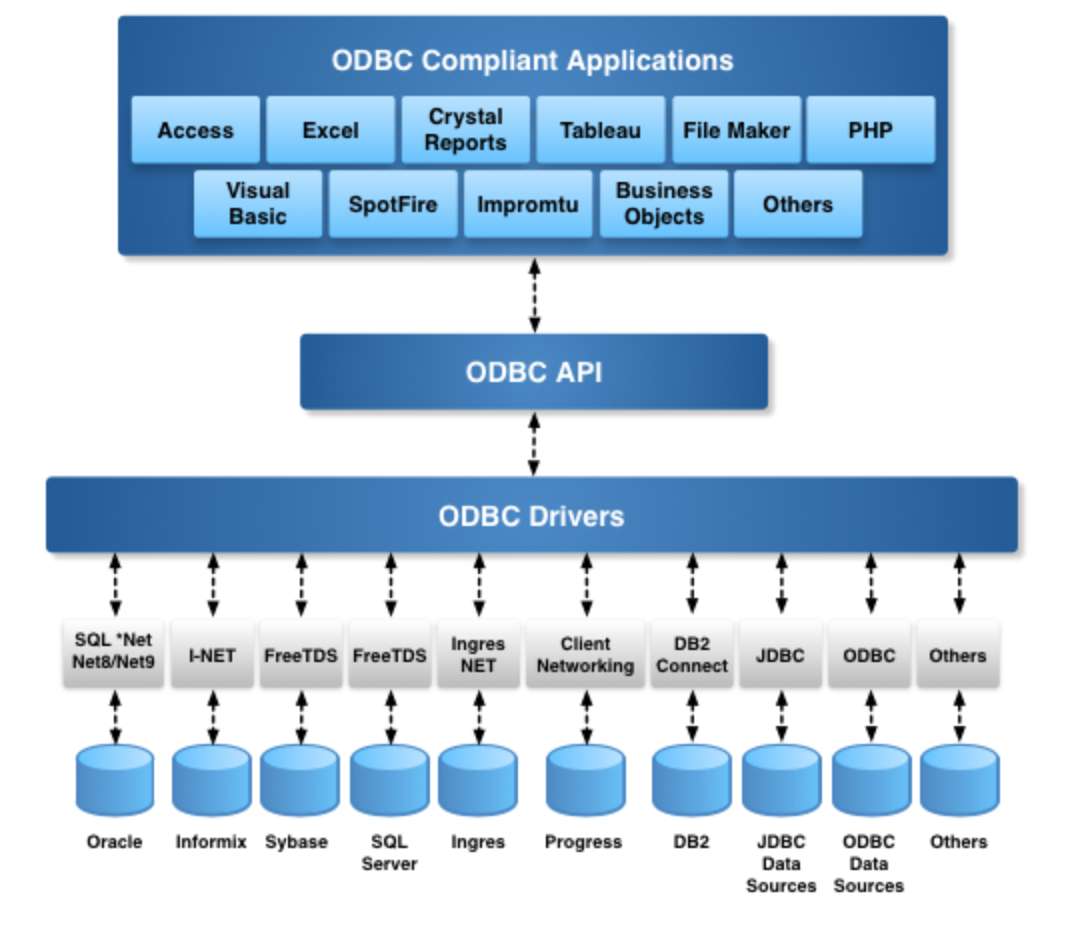
ODBC Connector (Driver) Architecture
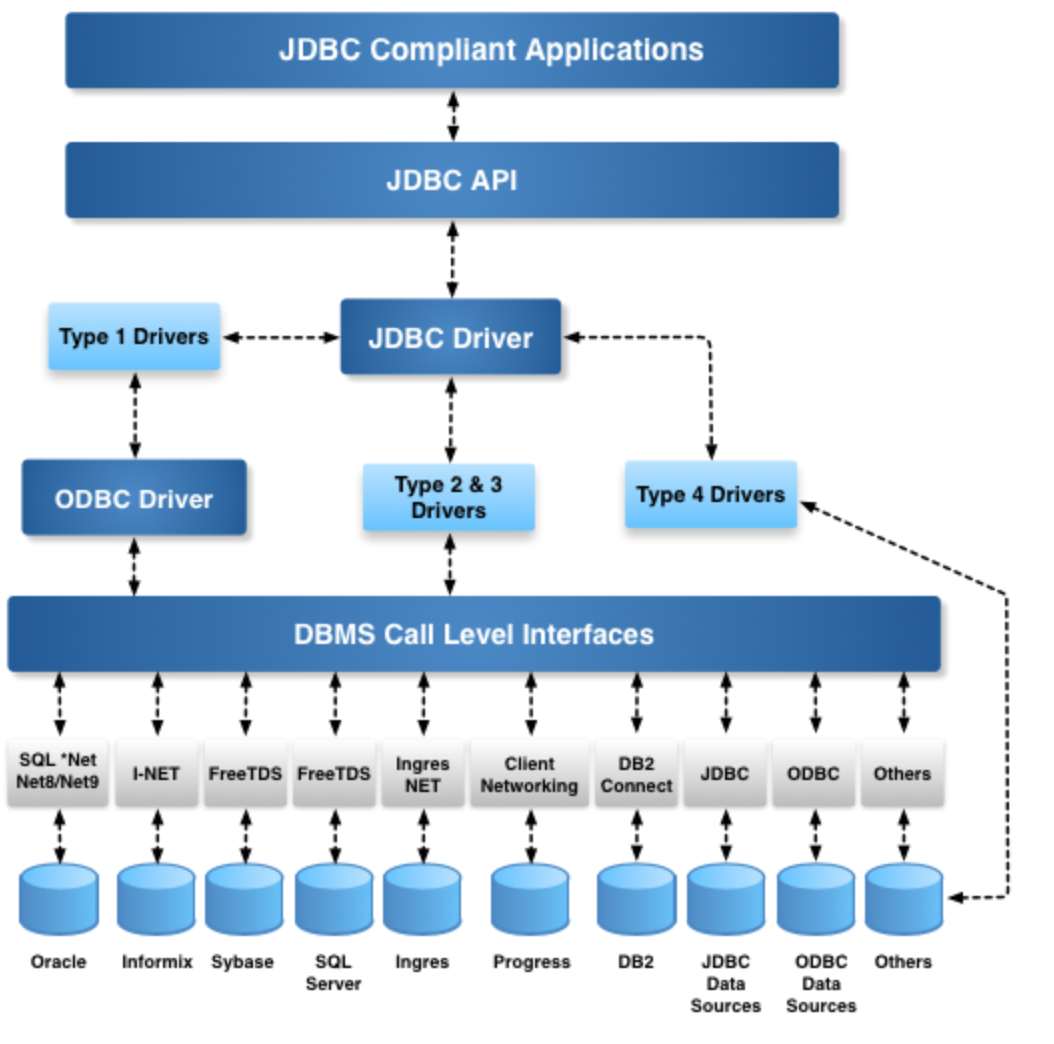
JDBC Connector (Driver) Architecture
Understanding Database Connector Challenges
Database connectors are designed to facilitate seamless communication between applications and databases. While this may sound straightforward, the reality is far more intricate. Here are some key features that highlight why enterprise-grade connectors, like those from OpenLink, far surpass free alternatives:
1. Escape Syntaxes for Dates and Functions
Free connectors often lack the necessary abstraction layers to handle date formats and function call signatures seamlessly across different databases. OpenLink connectors provide robust solutions that standardize these operations, ensuring efficiency and consistency.
2. Metadata Calls
Smart applications depend heavily on metadata calls, which free connectors typically under-implement. Enterprise-grade connectors provide comprehensive metadata access, eliminating the need for applications to be DBMS-specific.
3. Scrollable Cursors
Handling large datasets efficiently requires advanced cursor support. Free connectors frequently “fake” cursor support, leading to performance and integrity issues. OpenLink connectors fully support essential cursor types, including:
-
Static
-
Forward-Only
-
Key-Set
-
Dynamic
-
Mixed models
The Imperative Nature of Data Security
Beyond technical intricacies, data security is a paramount concern. Paid connectors offer robust security mechanisms that free alternatives simply cannot match:
Attribute-Based Access Controls (ABAC)
Our connectors natively support ABAC, a security framework that enables fine-grained access control based on:
-
Users & User Groups – Restrict access based on identity.
-
Specific Databases & Applications – Define policies tailored to individual data sources.
-
Client Host Operating Systems & IP Ranges – Allow or deny connections based on network attributes.
This level of access control ensures protection against unauthorized access, a growing concern in today’s cybersecurity landscape.
The OpenLink Connector Advantage
OpenLink’s enterprise edition connectors are built using a multi-tier architecture, ensuring high performance, stability, and strict adherence to industry standards. Unlike free connectors that provide only basic functionality, OpenLink connectors go beyond connectivity by integrating security, performance optimizations, and compatibility enhancements.
Security Use Case: Preventing Unauthorized Database Access
In today’s environment, phishing attacks frequently result in compromised credentials, providing unauthorized access to private databases. OpenLink’s ABAC functionality allows administrators to enforce policies such as:
-
Restricting read access to connections originating from specific network addresses within an approved range.
-
Defining access policies based on user, application, and network parameters.
-
Granular control over read-write permissions, limiting database modifications to authorized users only.
This policy-driven security model ensures that even if credentials are stolen, unauthorized users cannot exploit them outside predefined conditions.

OpenLink Secure Enterprise Edition Connectors leveraging Multi-Tier Architecture
Final Thoughts
While free connectors might seem appealing from a cost perspective, the value, security, and performance offered by enterprise-grade connectors—especially those from OpenLink—far outweigh the initial savings. In an era where data is an organization’s most valuable asset, securing and optimizing access should never be left to chance.