This guide outlines steps required for generating a Link-In-Bio variant of a Personal Profile Document, comprising public credentials that ultimately aid user-controlled self-sovereign identity.
Completing the process below will put you in position to use the YouID Credential Generator, either the browser extension or the iOS app, to achieve the following goals:
-
Generate a Link-In-Bio-style Personal Profile Document.
-
Use credentials in the Profile Document to respond to Identity Authentication challenges when trying to access protected resources from your desktop, notebook, or mobile computing device via HTTPS.
Step-by-Step Guide
Generate a Profile Document
-
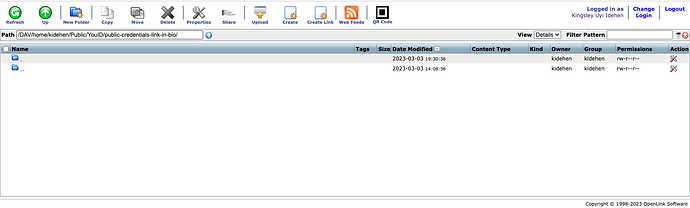
Create a folder, like
https://kingsley.idehen.net/DAV/home/kidehen/Public/YouID/public-credentials-link-in-bio/ -
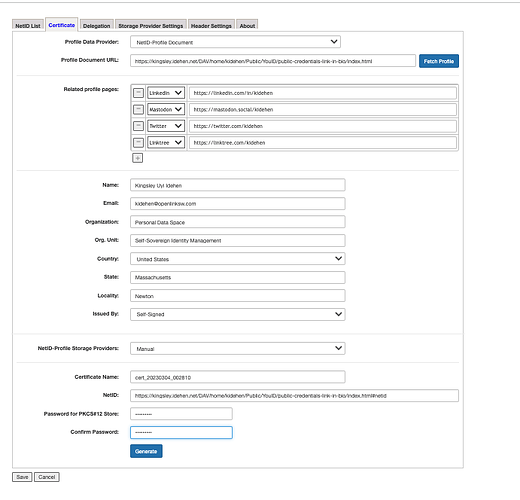
Assume your PdP is going to be
https://kingsley.idehen.net/DAV/home/kidehen/Public/YouID/public-credentials-link-in-bio/index.html -
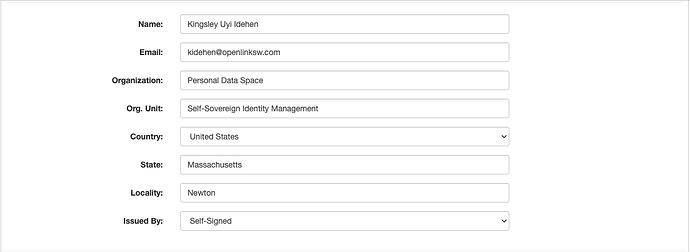
Provide the PdP URL to YouID
-
Complete the rest of the form
-
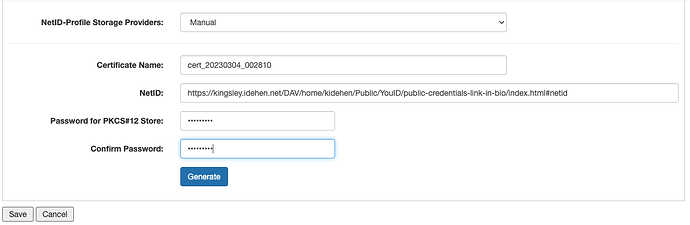
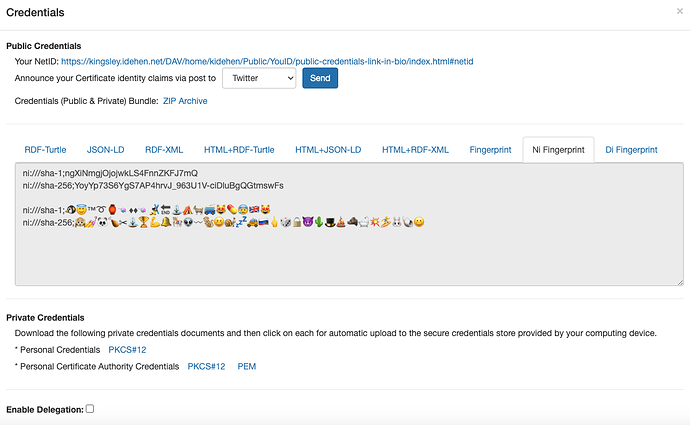
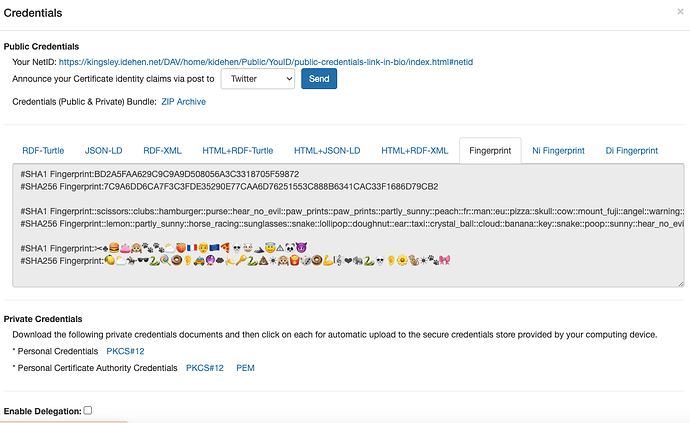
Generate your Credentials
-
Download Zip Archive
Generated Credentials Publication
-
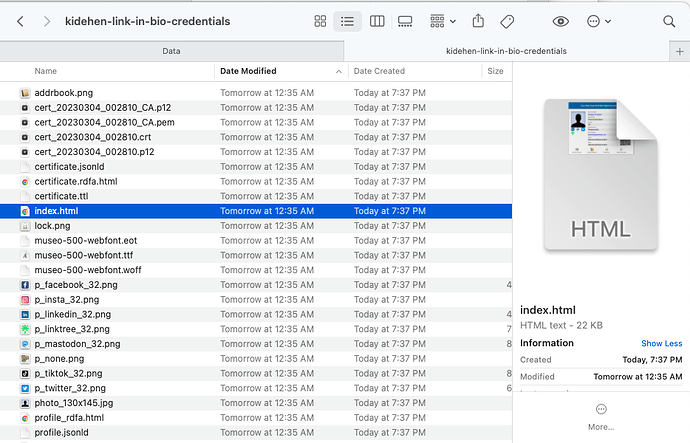
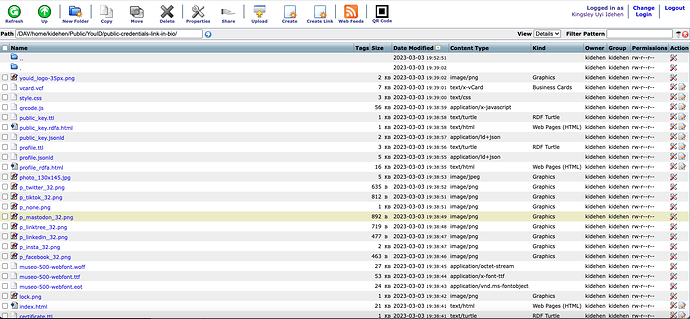
Unzip Archive
-
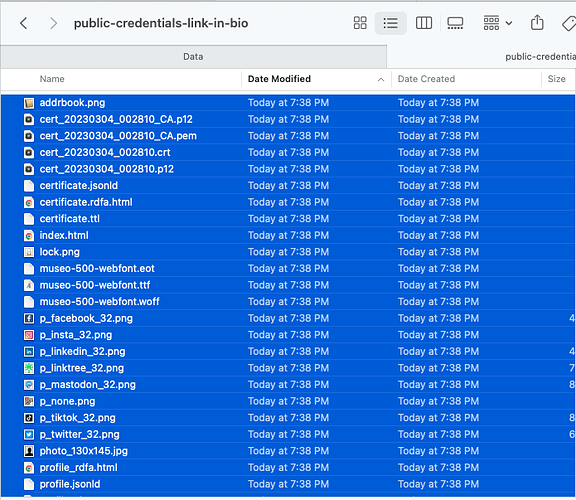
Mount a designated remote HTTP+WebDAV accessible folder to your desktop OS i.e., the same folder created in step 1 of the Credentials Generation Section
-
Copy all the files extracted from the ZIP archive to the WebDAV folder mounted in the previous step
-
Use your browser to view the files in the remote WebDAV location
-
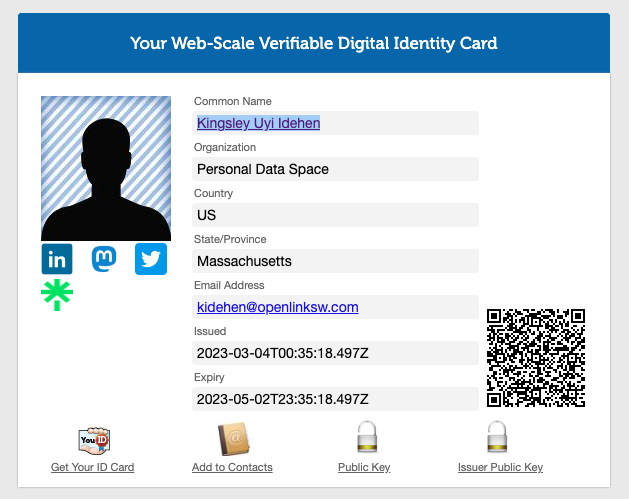
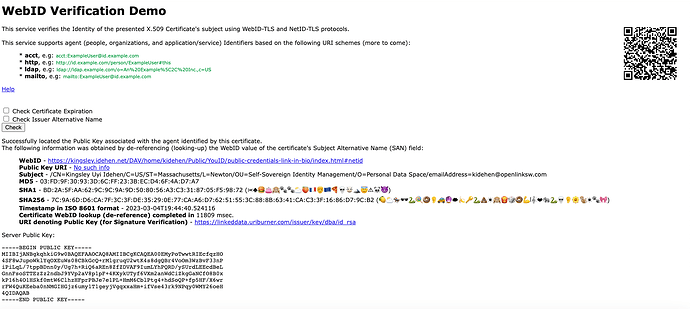
Verify that your newly generated NetID resolves, by clicking your variant of
https://kingsley.idehen.net/DAV/home/kidehen/Public/YouID/public-credentials-link-in-bio/index.html#netid
Registering a NetID with YouID’s browser-hosted credential store (also referred to as a wallet)
Note: The following steps only apply to the YouID Browser Extension (not to the YouID hosted service).
-
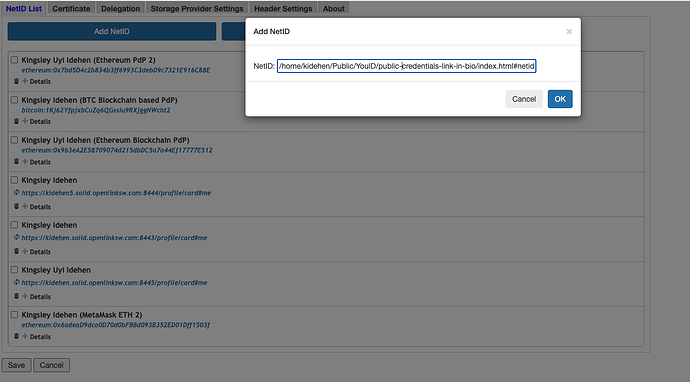
Add your variant of
https://kingsley.idehen.net/DAV/home/kidehen/Public/YouID/public-credentials-link-in-bio/index.html#netidto your YouID-managed NetID List.
Private Credentials Storage
-
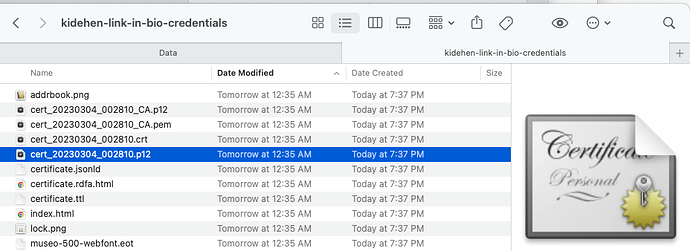
Locate the private credentials from the secure PKCS#12 file (situated in the folder created when you unzipped the YouID generated ZIP archive)
-
macOS Filesystem View of Secure PKCS#12 Credentials Document
-
-
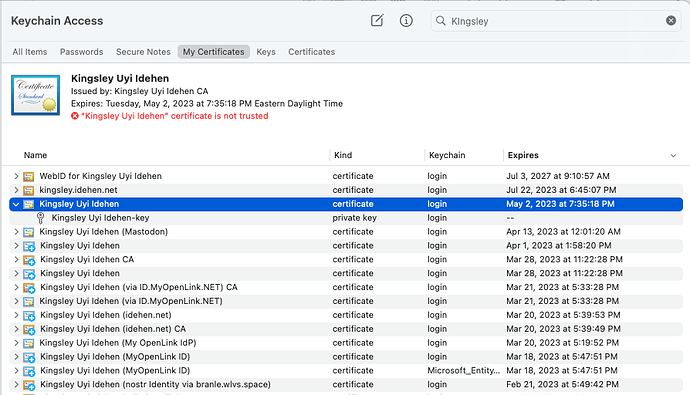
Open the secure PKCS#12 credentials file using the mechanism provided by your host operating system (commonly a double-click, since every modern operating system understands this secure file format)
-
macOS
Keychain.appView of Secure PKCS#12 Credentials Document -
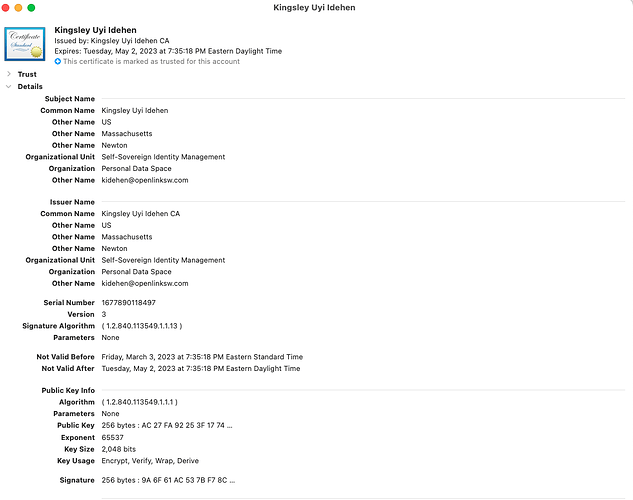
macOS
Keychain.appView of Credentials Notarized by an X.509 Certificate -
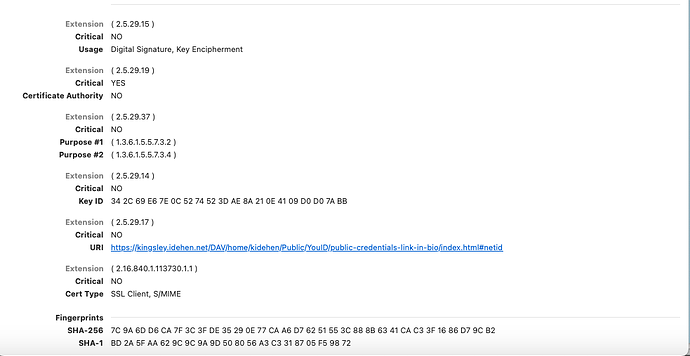
macOS
Keychain.appView of Credentials Notarized by an X.509 Certificate Contd
-
If you plan to send self-signed emails using Apple Mail or Microsoft OutLook, repeat these steps for the Certificate Authority (CA) secure PKCS#12. If you plan to use Thunderbird, you will only need to load the CA’s .pem file when prompted during the configuration process for your email account.
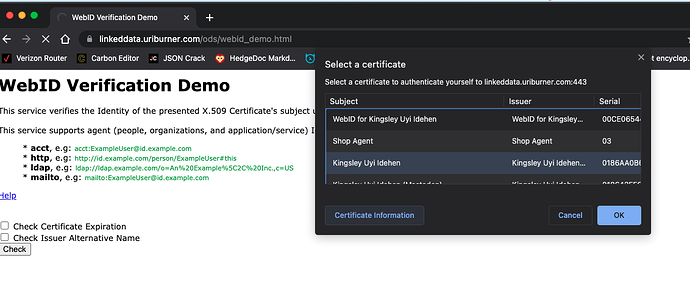
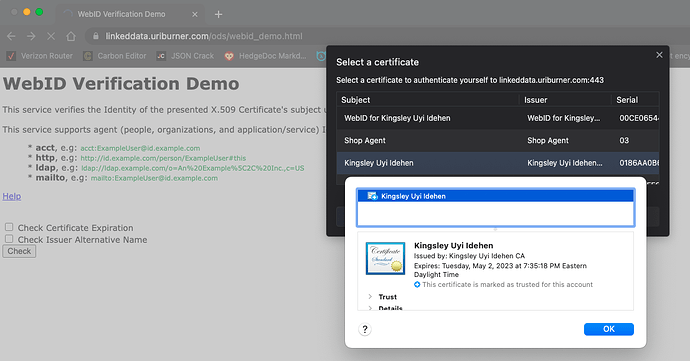
Credentials Verification
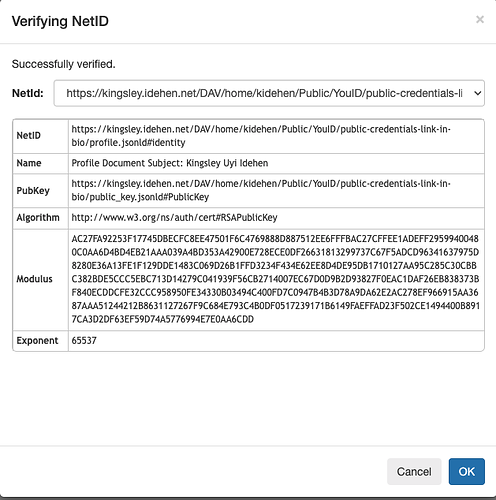
This is achieved by a NetID-TLS verification service (at an endpoint), that implements Client Certificate Authentication using an extended session initialization handshake along the following lines:
-
De-references the hyperlink used to denote the subject of the X.509 certificate used in the session initialization to a publicly-accessible profile document comprising a public credentials mirror, i.e., a Public Key, Public Key SHA-1 hash, etc.
-
Compares the public and private credentials to ensure a match
-
Returns a publicly-accessible signed certification document, if the credentials match
Conclusion
As demonstrated in this post, each YouID release reduces the friction associated with Self-Sovereign Identity that’s fully controlled by end-users rather than technology vendors.
End-users can now take advantage of the following without any third-party dependencies:
- Issue X.509 Certificates that can be used to digitally sign and/or encrypt emails using the S/MIME protocol — supported by all modern email applications across desktops, notebooks, or mobile phones
- Generate Link In Bio profile documents comprising verifiable credentials that manifest a powerful Personal Profile Knowledge Graph, without any limitations applied to additional profile document cross-references
Availability
- …for Chrome, Brave, Opera, and other compatible browsers
- …for Firefox
- …for Safari (working its way through App Store Review)
- …for iOS on iPhone or iPad (coming soon!)